Are our cars spying on us? A cybersecurity expert explains how to stay safe | UniSC

What data do these cars collect? Connected vehicles are packed with sensors: in the seats, the dashboard, the engine, the steering wheel. Many also have additional driver-facing cameras plus external cameras. Vehicles can generate 1 to 2 terabytes of raw data per car each day. Manufacturers collect sensor data to measure vehicle performance. However, collected […]
How to watch the king's speech like a pro – POLITICO

King Charles III will on Wednesday deliver a speech setting out Keir Starmer's legislative agenda. Here's what to look out for. Source link
The latest phishing scam? Fake party invitations

Who doesn’t love getting invited to a party? Unfortunately, scammers are now exploiting that excitement — and preying on your fear of missing out — with phishing emails disguised as digital invitations. Many of these emails spoof legitimate platforms such as Evite, Punchbowl, and Paperless Post. All three sites have recently issued warnings to users, […]
How to Organize Safely in the Age of Surveillance

For all these approaches, from the fully public to the paranoid, the same principle applies as in a Signal conversation: A piece of information is only as secure as the least secured device that accesses it. So as you consider your threat model and whose devices and accounts within your group have access to your […]
Artificial intelligence is fueling romance scams. Here’s how

Online dating can be challenging enough, but scammers are using artificial intelligence to sound more charming and believable. Americans lost more than $672 million from romance scams in 2024, according to a report by the Federal Bureau of Investigation. A.I. has only made these scams more widespread. One in four Americans say they’ve encountered a […]
How to protect personal information, as data breaches hit a new high
Fertnig | E+ | Getty Images It’s the letter most consumers dread receiving — the notification that your personal information has been involved in a data breach. About 80% of respondents to a new survey said they received at least one data breach notice in the prior 12 months, according to the Identity Theft Resource […]
How to Protect Your iPhone or Android Device From Spyware

Infection usually starts through malicious links and fake apps, but it is also taking place via “more subtle methods,” says Richard LaTulip, a field CISO at security company Recorded Future, which collaborated with Google’s threat intelligence team on the Predator spyware findings. LaTulip cites the example of recent research on malicious browser extensions affecting millions […]
What Is a Passkey? Here’s How to Set Up and Use Them (2025)

With a password, there’s a ton of room for an attacker to potentially steal your password. Data breaches might expose your password, and even if it’s encrypted, it can be cracked. Phishing schemes are an easy vector of attack for hackers looking to steal passwords. And, if you’re using a service with spotty security practices, […]
A Researcher Figured Out How to Reveal Any Phone Number Linked to a Google Account

A cybersecurity researcher was able to figure out the phone number linked to any Google account, information that is usually not public and is often sensitive, according to the researcher, Google, and 404 Media’s own tests. The issue has since been fixed but at the time presented a privacy issue in which even hackers with […]
How to Win Followers and Scamfluence People
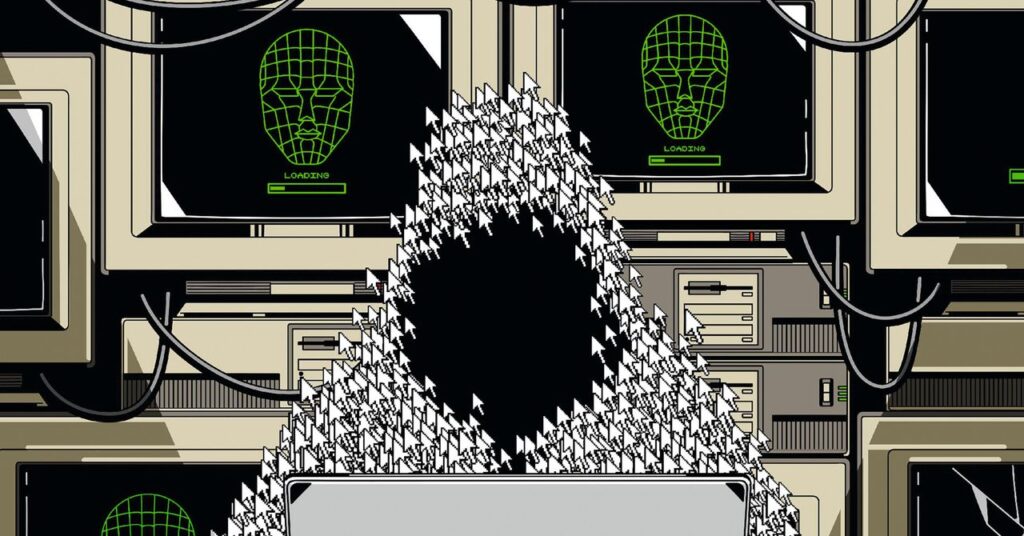
As soon as Format Boy answers the phone, I recognize his booming voice. I’ve spent weeks immersed in the influencer’s back catalog of videos and voice notes. Format Boy isn’t like other influencers: He doesn’t show his face, and he won’t tell me his real name. He isn’t posting motivational content or seeking lucrative brand […]