How to Organize Safely in the Age of Surveillance

For all these approaches, from the fully public to the paranoid, the same principle applies as in a Signal conversation: A piece of information is only as secure as the least secured device that accesses it. So as you consider your threat model and whose devices and accounts within your group have access to your […]
How to Protect Your iPhone or Android Device From Spyware

Infection usually starts through malicious links and fake apps, but it is also taking place via “more subtle methods,” says Richard LaTulip, a field CISO at security company Recorded Future, which collaborated with Google’s threat intelligence team on the Predator spyware findings. LaTulip cites the example of recent research on malicious browser extensions affecting millions […]
How to Use a Password Manager to Share Your Logins After You Die (2025)
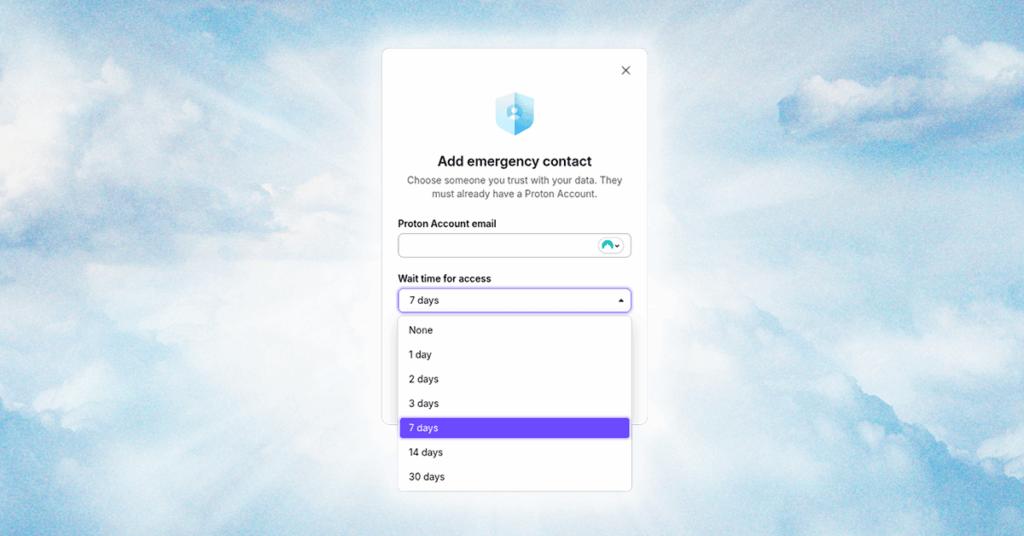
It’s not fun to talk about, but there’s only one thing certain in life. You need to have a plan for your digital legacy, just like you make a plan for your physical assets; otherwise, your accounts, services, and logins will rot away in a data center before they’re inevitably erased by a data retention […]
How to Use 1Password’s Travel Mode at the Border (2025)
Enter VeraCrypt. It’s a free, open source encryption app that can encrypt full drives, as well as operating system partitions, similar to BitLocker or FileVault. The big feature of VeraCrypt is plausible deniability. There are specific setup steps, but you can store an encrypted partition within an encrypted partition. When you encrypt a drive with […]
How to Set Up and Use a Burner Phone
When you are done with the burner phone, make sure that you get rid of it in a thoughtful way as well. “At the end of the intended use, consider steps to eliminate information, remove SIM cards and/or memory cards, making sure not to leave a potential vulnerability after you,” says Access Now’s Al-Maskati. Using […]
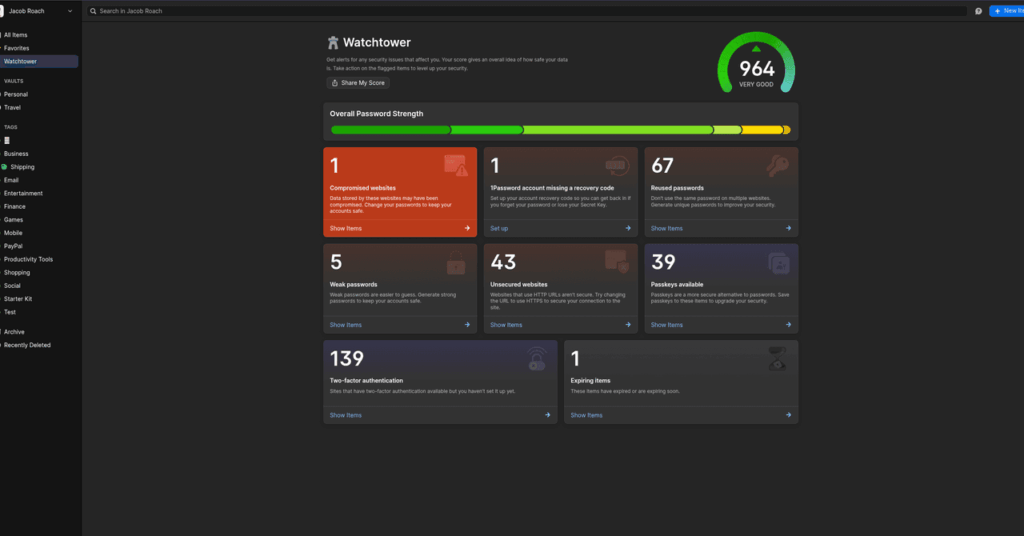
What Is a Passkey? Here’s How to Set Up and Use Them (2025)

With a password, there’s a ton of room for an attacker to potentially steal your password. Data breaches might expose your password, and even if it’s encrypted, it can be cracked. Phishing schemes are an easy vector of attack for hackers looking to steal passwords. And, if you’re using a service with spotty security practices, […]
How to Avoid US-Based Digital Services—and Why You Might Want To

Law enforcement requests for user data from Apple, Google, and Meta mean that these companies can decide whether government authorities have access to your personal information, including location data. This means the companies with the most insight into our lives, movements, and communications are frontline arbiters of our constitutional rights and the rights of non-US […]
The NSA Has a Podcast—Here's How to Decode It – WIRED

The NSA Has a Podcast—Here's How to Decode It. The spy agency that dared not speak its name is now the Joe Rogan of the SIGINT set. And the pod's … Source link
How Apple’s Advanced Data Protection Works, and How to Enable It on Your iPhone

ADP extends that protection pretty considerably to also cover your iCloud backups, iCloud Drive, and the information in Photos, Notes, and Reminders. Without ADP enabled, this data is still encrypted, which adds a strong layer of protection from third parties or bad actors. But Apple can still access this data and turn it over to […]