Video Doorbell Advice and Settings for Opting Out of the Surveillance State

There’s also the risk that footage falls into the wrong hands and ends up enabling politically-motivated investigations, police harassment, or stalking without you intending or even knowing about it. Maybe company employees or third-party contractors gain access to videos, or your cameras are hacked. Amazon settled a privacy lawsuit brought by the FTC that mentioned […]
How to Organize Safely in the Age of Surveillance

For all these approaches, from the fully public to the paranoid, the same principle applies as in a Signal conversation: A piece of information is only as secure as the least secured device that accesses it. So as you consider your threat model and whose devices and accounts within your group have access to your […]
Don’t let AI chatbots tell you how to vote, Dutch authorities warn voters – POLITICO
Dutch voters elect a new parliament next Wednesday. The Dutch data protection authority ran an experiment on how parties were portrayed in voting advice across four different chatbots, including OpenAI’s ChatGPT, Google’s Gemini, Elon Musk’s Grok and French Mistral AI’s Le Chat. The authority set up profiles that matched different political parties (based on vetted […]
How to Use Passkeys With Google Password Manager (2025)
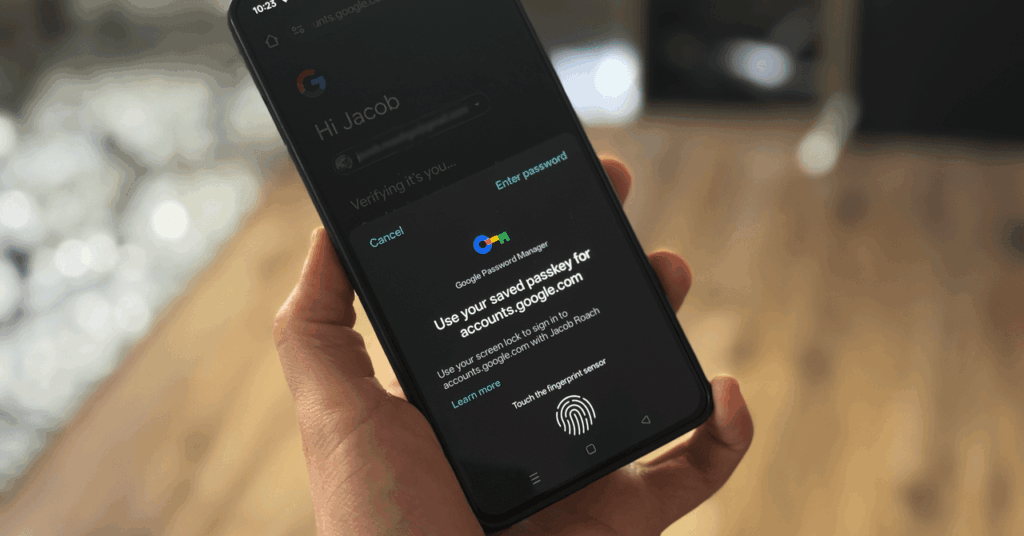
Google wants you to start using passkeys. Its vision is to “progress toward a passwordless future,” allowing you to store passkeys in the Google Password Manager service. For websites that support the login method, Google now allows you to generate, store, and sync passkeys. The problem is actually finding a consistent way to do it. […]
Anthropic Will Use Claude Chats for Training Data. Here’s How to Opt Out
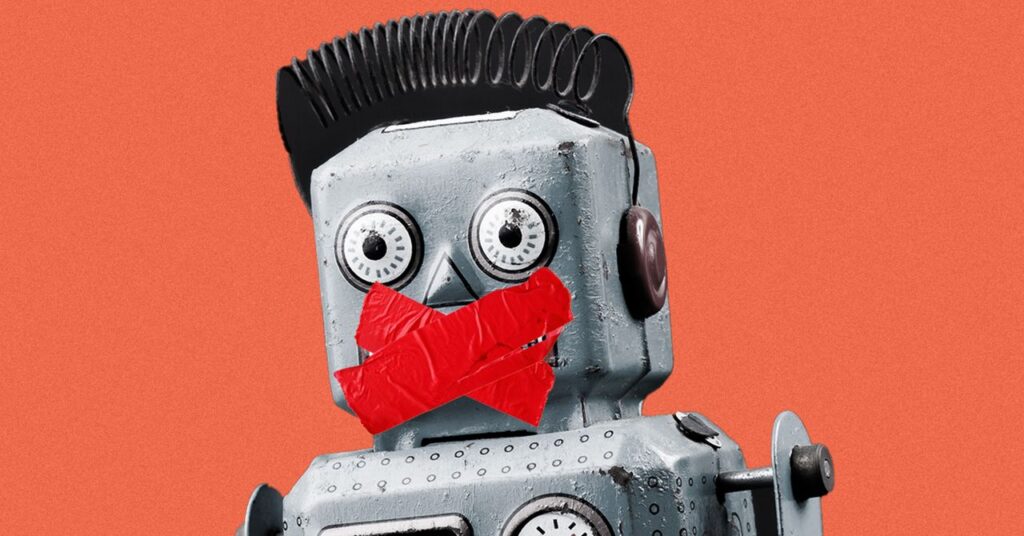
Anthropic is prepared to repurpose conversations users have with its Claude chatbot as training data for its large language models—unless those users opt out. Previously, the company did not train its generative AI models on user chats. When Anthropic’s privacy policy updates on October 8 to start allowing for this, users will have to opt […]
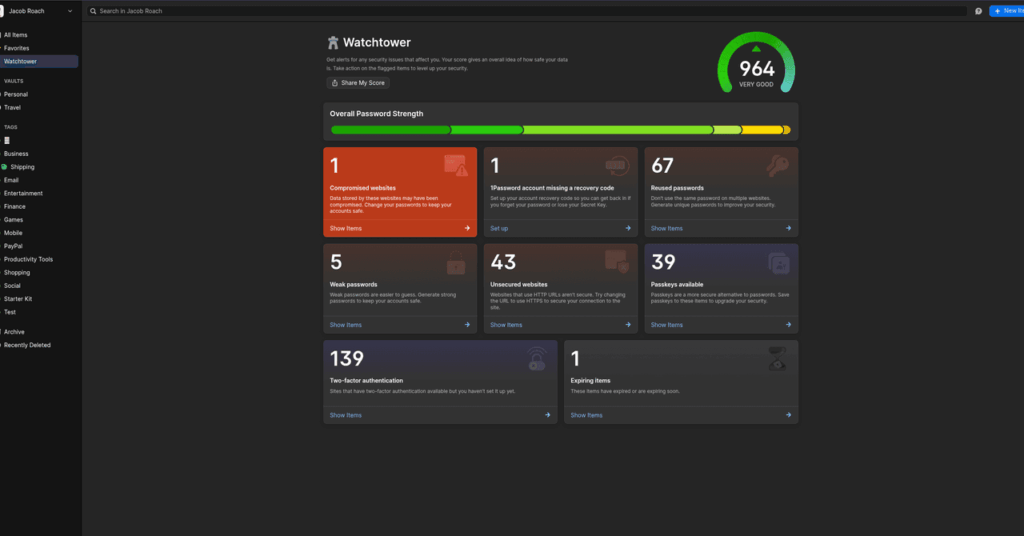
How to Use a Password Manager to Share Your Logins After You Die (2025)
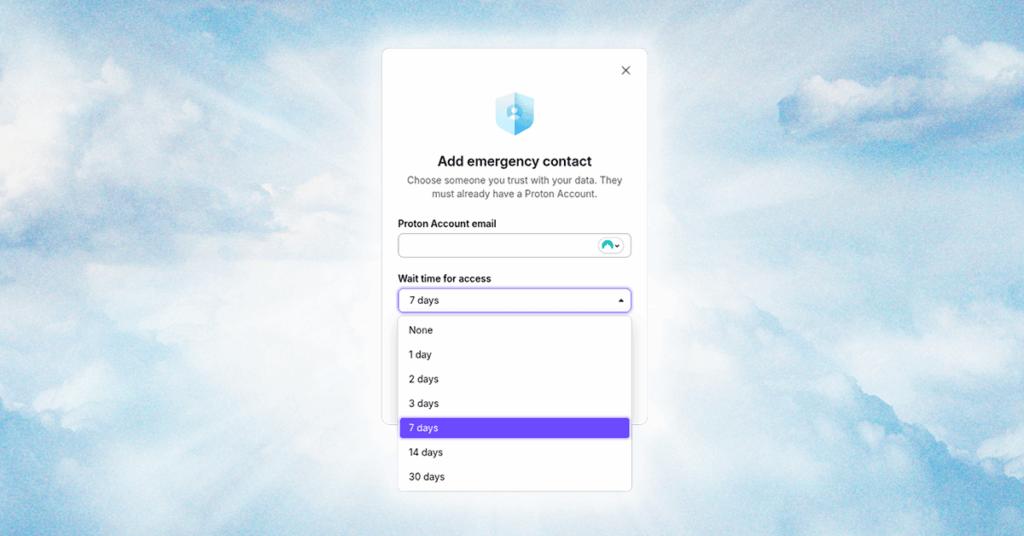
It’s not fun to talk about, but there’s only one thing certain in life. You need to have a plan for your digital legacy, just like you make a plan for your physical assets; otherwise, your accounts, services, and logins will rot away in a data center before they’re inevitably erased by a data retention […]
How to Use 1Password’s Travel Mode at the Border (2025)
Enter VeraCrypt. It’s a free, open source encryption app that can encrypt full drives, as well as operating system partitions, similar to BitLocker or FileVault. The big feature of VeraCrypt is plausible deniability. There are specific setup steps, but you can store an encrypted partition within an encrypted partition. When you encrypt a drive with […]
How to Set Up and Use a Burner Phone
When you are done with the burner phone, make sure that you get rid of it in a thoughtful way as well. “At the end of the intended use, consider steps to eliminate information, remove SIM cards and/or memory cards, making sure not to leave a potential vulnerability after you,” says Access Now’s Al-Maskati. Using […]
What Is a Passkey? Here’s How to Set Up and Use Them (2025)

With a password, there’s a ton of room for an attacker to potentially steal your password. Data breaches might expose your password, and even if it’s encrypted, it can be cracked. Phishing schemes are an easy vector of attack for hackers looking to steal passwords. And, if you’re using a service with spotty security practices, […]
How to protect your cookies from theft

When you visit almost any website, you’ll see a pop-up asking you to accept, decline, or customize the cookies it collects. Sometimes, it just tells you that cookies are in use by default. We randomly checked 647 websites, and 563 of them displayed cookie notifications. Most of the time, users don’t even pause to think […]