How to watch the king's speech like a pro – POLITICO

King Charles III will on Wednesday deliver a speech setting out Keir Starmer's legislative agenda. Here's what to look out for. Source link
How to Disable Google’s Gemini in Chrome
If you use Google’s Chrome browser for desktop, there’s probably a Gemini Nano AI model running on your computer right now and taking up about 4 GB of space. That’s not necessarily a bad thing, but if you didn’t know about it and don’t want it, there’s a way to turn it off. The file […]
How to watch Romania’s political chaos like a pro – POLITICO

If Bolojan loses the vote he will be out as prime minister. Independent centrist President Nicușor Dan will then begin consultations with party leaders to form a new coalition government, with a new prime minister. In that case, one possibility is that the coalition between Bolojan’s liberals and the social democrats carries on but with […]
How to Avoid Getting Locked Out of Your Google Account

Many of us have a lot of digital data locked away in our Google accounts: emails, photos, chats, documents, schedules, restaurant reviews. Losing access to that data is likely to be fairly high on the catastrophe scale. There are steps you can take before that happens to minimize the chances of you and your Google […]
Video Doorbell Advice and Settings for Opting Out of the Surveillance State

There’s also the risk that footage falls into the wrong hands and ends up enabling politically-motivated investigations, police harassment, or stalking without you intending or even knowing about it. Maybe company employees or third-party contractors gain access to videos, or your cameras are hacked. Amazon settled a privacy lawsuit brought by the FTC that mentioned […]
How to Prepare for Tomorrow’s Wars by James Ryseff

en English Politics Feb 25, 2026 James Ryseff Just as established corporations facing challenges from innovative startups must adapt or die, militaries must continually renew themselves to remain effective against emerging threats. For democracies today, this means investing in evolving technologies and embracing new ways of operating. WASHINGTON, DC – We are living through a […]
How to Organize Safely in the Age of Surveillance

For all these approaches, from the fully public to the paranoid, the same principle applies as in a Signal conversation: A piece of information is only as secure as the least secured device that accesses it. So as you consider your threat model and whose devices and accounts within your group have access to your […]
How to Protect Your iPhone or Android Device From Spyware

Infection usually starts through malicious links and fake apps, but it is also taking place via “more subtle methods,” says Richard LaTulip, a field CISO at security company Recorded Future, which collaborated with Google’s threat intelligence team on the Predator spyware findings. LaTulip cites the example of recent research on malicious browser extensions affecting millions […]
How to Set Up a Google Home Security System: Best Cameras, Doorbells, and Other Devices
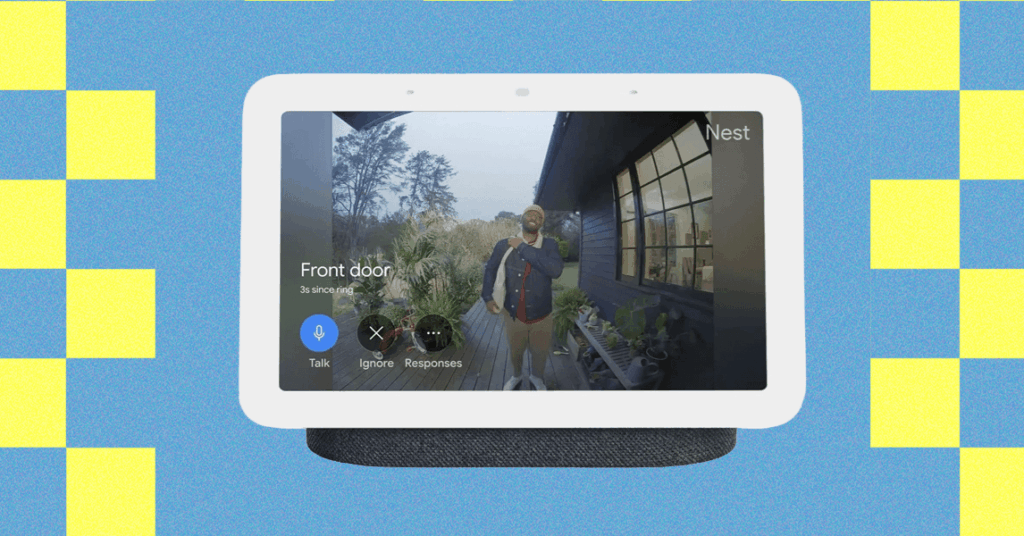
There’s no need for an expensive, professionally installed home security system for a little peace of mind. You can keep tabs on your home when you’re away, check in on your kids or pets, and discourage intruders with a few well-placed security cameras and connected devices. Easily the smartest option on the market right now, […]
How to Use Passkeys With Google Password Manager (2025)
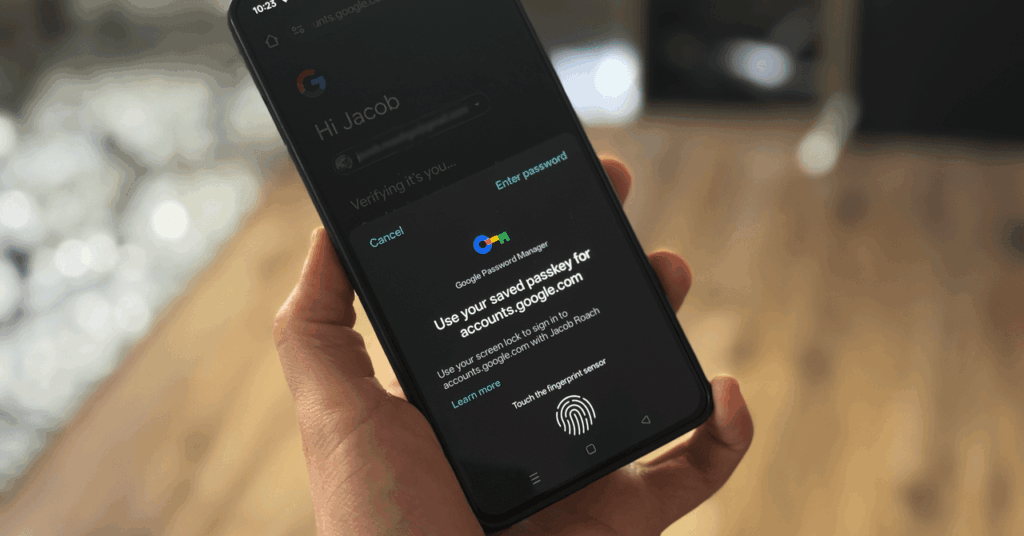
Google wants you to start using passkeys. Its vision is to “progress toward a passwordless future,” allowing you to store passkeys in the Google Password Manager service. For websites that support the login method, Google now allows you to generate, store, and sync passkeys. The problem is actually finding a consistent way to do it. […]