How to Use a Password Manager to Share Your Logins After You Die (2025)
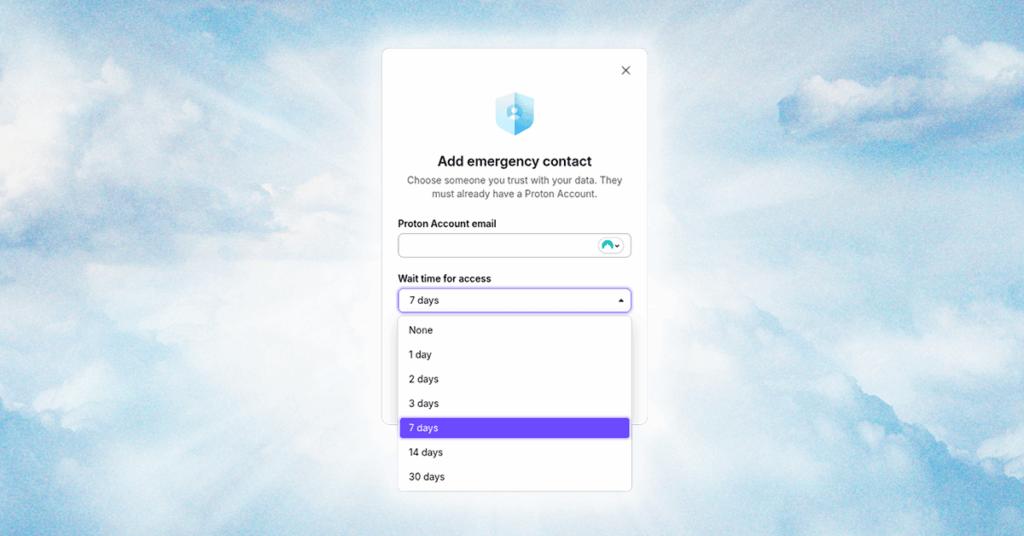
It’s not fun to talk about, but there’s only one thing certain in life. You need to have a plan for your digital legacy, just like you make a plan for your physical assets; otherwise, your accounts, services, and logins will rot away in a data center before they’re inevitably erased by a data retention […]
How to Use 1Password’s Travel Mode at the Border (2025)
Enter VeraCrypt. It’s a free, open source encryption app that can encrypt full drives, as well as operating system partitions, similar to BitLocker or FileVault. The big feature of VeraCrypt is plausible deniability. There are specific setup steps, but you can store an encrypted partition within an encrypted partition. When you encrypt a drive with […]
How to Set Up and Use a Burner Phone
When you are done with the burner phone, make sure that you get rid of it in a thoughtful way as well. “At the end of the intended use, consider steps to eliminate information, remove SIM cards and/or memory cards, making sure not to leave a potential vulnerability after you,” says Access Now’s Al-Maskati. Using […]
How to set up Single Sign-On in AWS (IAM Identity Center)
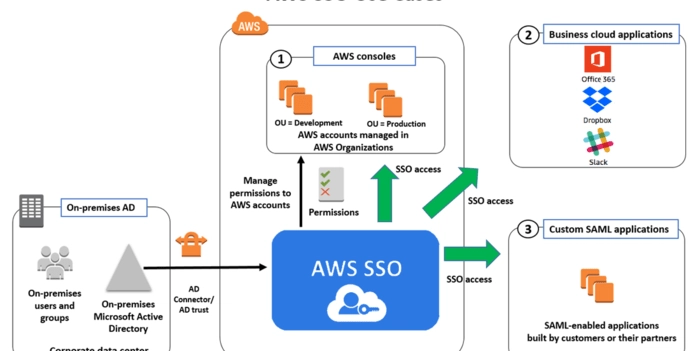
When I was at university, I met some programmers who were finishing their software engineering degrees. Some of them were already working, and they gave me what is still one of the best pieces of advice I’ve ever received about this craft: “If you want to be good, stick with university knowledge. If you want […]
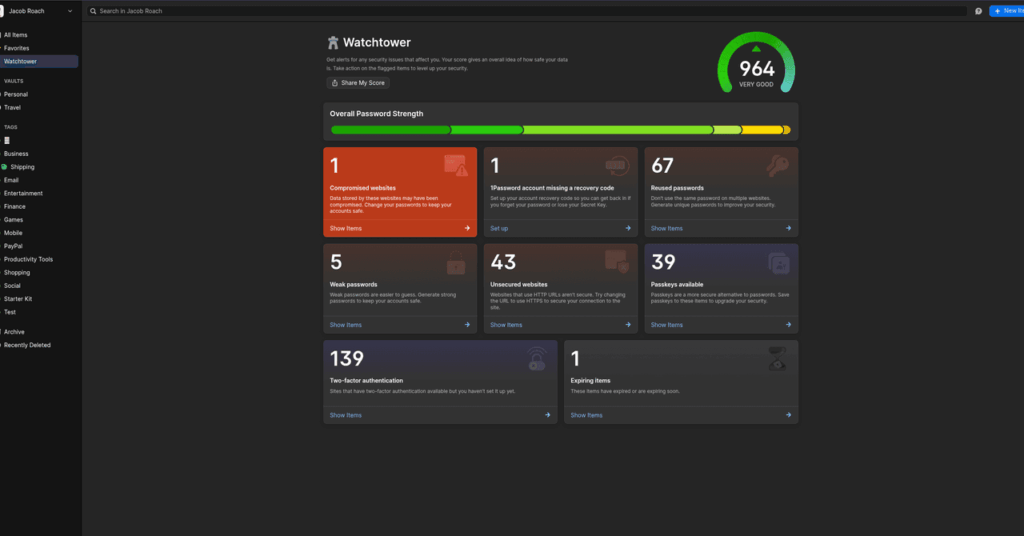
What Is a Passkey? Here’s How to Set Up and Use Them (2025)

With a password, there’s a ton of room for an attacker to potentially steal your password. Data breaches might expose your password, and even if it’s encrypted, it can be cracked. Phishing schemes are an easy vector of attack for hackers looking to steal passwords. And, if you’re using a service with spotty security practices, […]
How to Spot and Guard Against Wrong Number Scams
Most often, once some kind of friendship or even romantic connection has been established, you’ll be asked for money. Maybe your new contact is in a bit of trouble, finance-wise, and just needs a quick loan; or maybe they’ve found a fantastic investment opportunity for you, though you’ll need to act very quickly to take […]
You can blur your home on Google Maps: Here's how to do it — and why

As homeowners invest in high-end locks, alarm systems and surveillance cameras to safeguard their properties, some law enforcement officials say … Source link
A Researcher Figured Out How to Reveal Any Phone Number Linked to a Google Account

A cybersecurity researcher was able to figure out the phone number linked to any Google account, information that is usually not public and is often sensitive, according to the researcher, Google, and 404 Media’s own tests. The issue has since been fixed but at the time presented a privacy issue in which even hackers with […]
How to watch the Polish presidential election like a pro – POLITICO

The presidential race will have a big say on whether Poland plays in the EU’s big league or if it retreats back into isolation alongside other populist-governed countries in Central Europe like Hungary and Slovakia. During PiS’s eight years in power it got into fights with the EU and other allies over efforts to politicize […]
How to stop your phone from secretly tracking you
Rossen Reports: How to stop your phone from secretly tracking you Updated: 5:10 PM EDT Apr 30, 2025 Your phone may be secretly tracking your movements through features like “Significant Locations” and the “Journaling” app, which record where you’ve been and access your personal data.Screenshots from a personal iPhone reveal visits to a Mexican restaurant, […]